A Stack is the first thing deployed in a customer’s cloud account when an install is created. It is an infrastructure template that provisions the foundational resources needed to deploy and operate the app. For each install, Nuon generates a Stack template in both Terraform and the platform’s native IaC language. Both formats produce the same resources, so you or your customer can use whichever one fits into your tooling and processes the best.Documentation Index
Fetch the complete documentation index at: https://docs.nuon.co/llms.txt
Use this file to discover all available pages before exploring further.
- On AWS, the native format is a CloudFormation stack.
- On Azure, the native format is an Azure Resource Manager (Bicep) deployment.
- On GCP, only Terraform is generated — Google Cloud’s Infrastructure Manager runs Terraform natively.
What does a Stack create?
A Stack provisions:- Networking by creating a new VPC or connecting to an existing one provided by the customer
- The Runner as a VM with Docker running the Runner binary
- IAM roles and permissions for the Runner to operate
How is a Stack deployed?
When a vendor creates an install, Nuon generates Stack templates (Terraform and the platform’s native IaC, where applicable) along with links and CLI snippets the vendor can share with the customer. The customer deploys whichever format fits their tooling using their own credentials. This is how access is granted: the customer creates the resources themselves. No cross-account access is required. The customer retains full ownership and visibility of all infrastructure created by the Stack.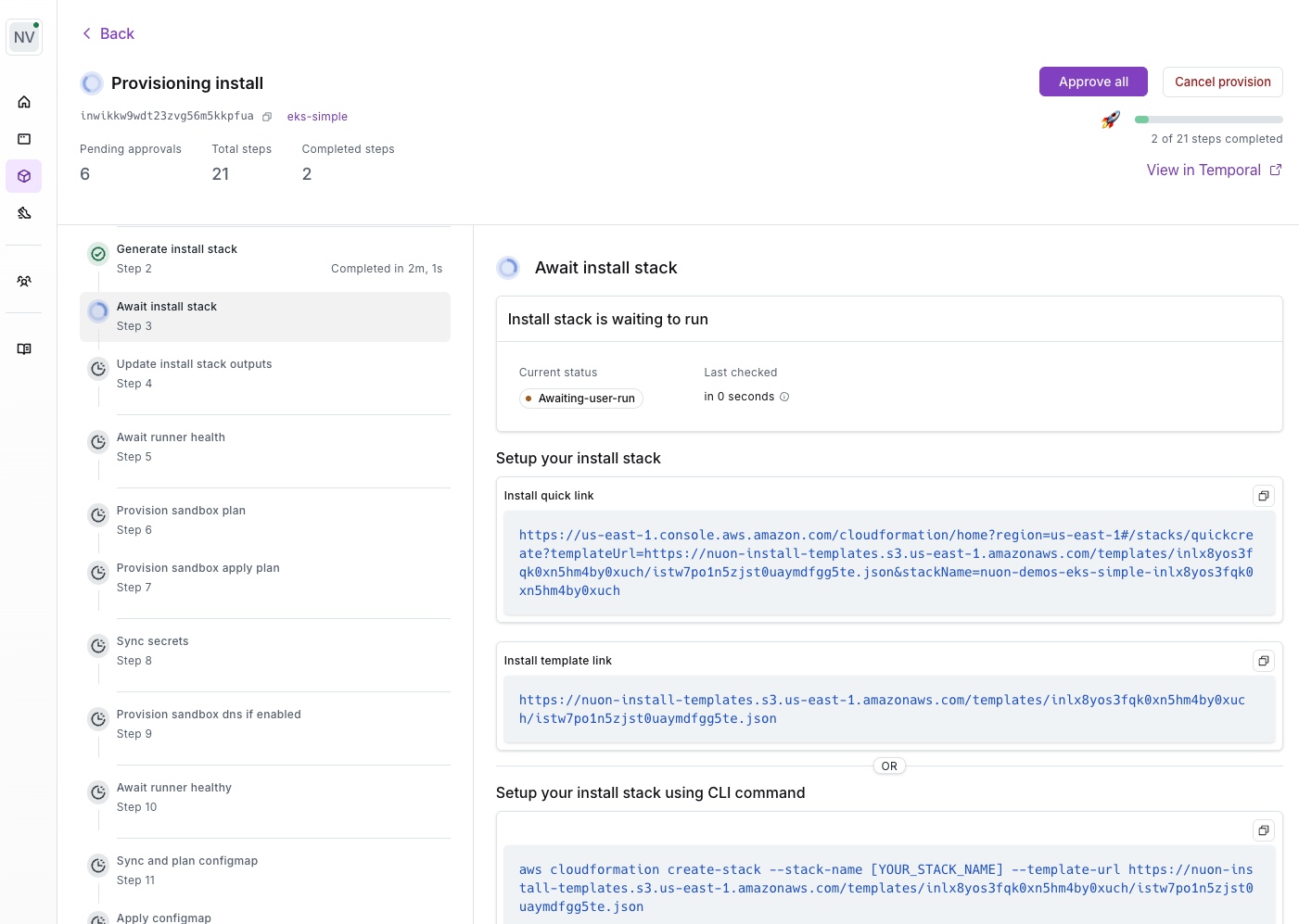
Customer Control
The Stack gives the customer full control over the Runner’s access. Through the stack parameters, the customer can:- Enable or disable the Runner to stop it from executing jobs
- Configure IAM roles and policies to control what the Runner can do
- Grant break glass roles for temporary elevated access during emergencies, which the customer can revoke at any time
Stack Inputs
Stacks can accept customer-provided values at deploy time. Secrets are entered by the customer when deploying the stack template (as CloudFormation parameters, Terraform variables, etc.) and are stored in the customer’s cloud secret manager (e.g., AWS Secrets Manager). Customer-facing inputs marked asuser_configurable are also passed through the stack.